Web-based vulnerability & business risk scoring
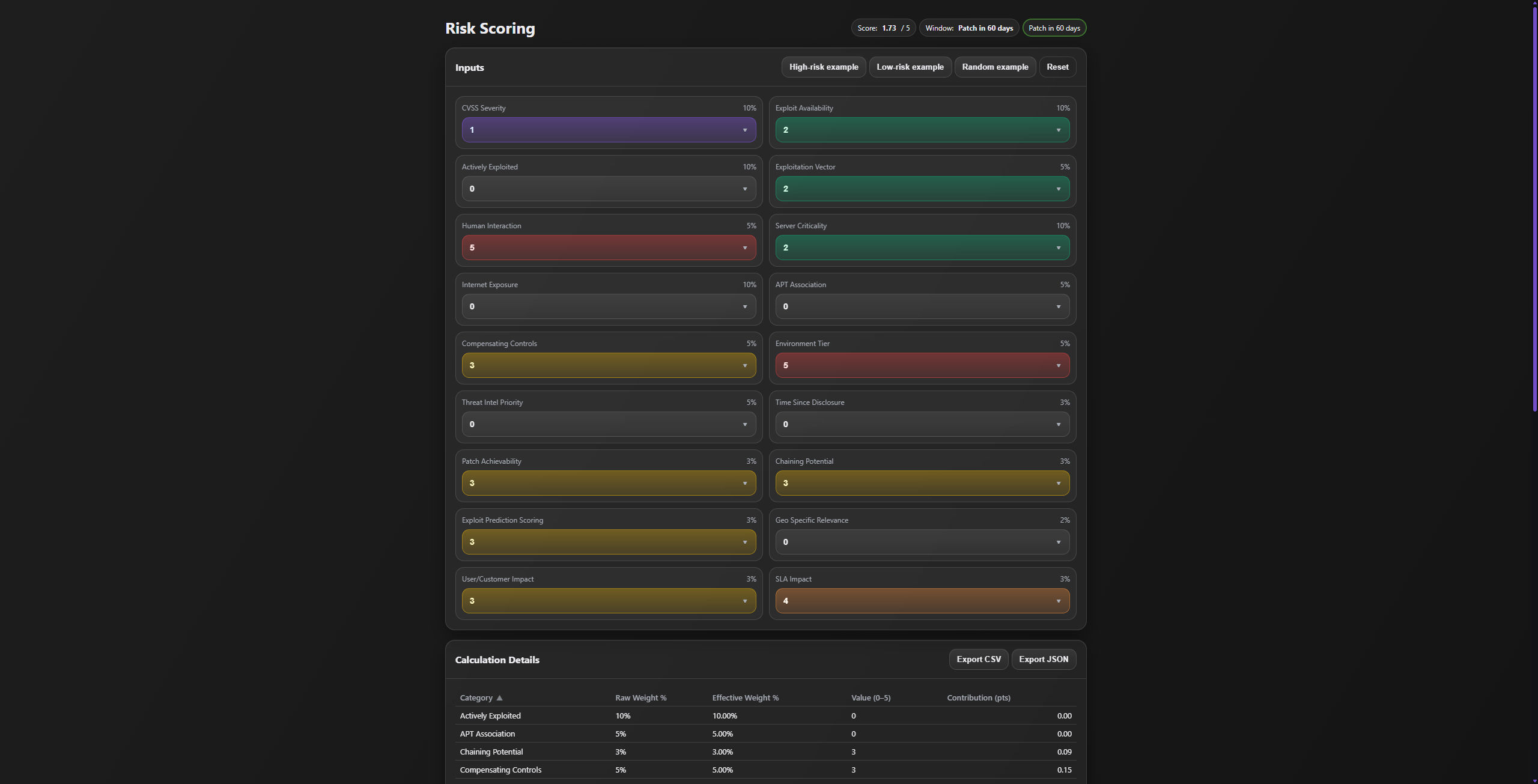
A lightweight risk scoring tool for assessing vulnerabilities on a 0–5 scale with category weighting, color-coded severity, sortable breakdowns, presets, and export to CSV/JSON.
tooling, labs, reverse engineering, and clean motion first UI.
I'm caleb, a Waikato based security minded systems engineer.
I recently completed a Bachelor of Information Technology with a focus
on cybersecurity, networking, and systems administration.
I spend a lot of time doing CTFs (HackTheBox, Crackmes, TryHackMe, NZCSC and more),
breaking and hardening lab environments, and building tooling to make
security tasks smoother.
Outside of keyboards and terminals, I'm into gaming, car projects
(my Mazda 6), and over engineering my homelab for fun.
A lightweight risk scoring tool for assessing vulnerabilities on a 0–5 scale with category weighting, color-coded severity, sortable breakdowns, presets, and export to CSV/JSON.
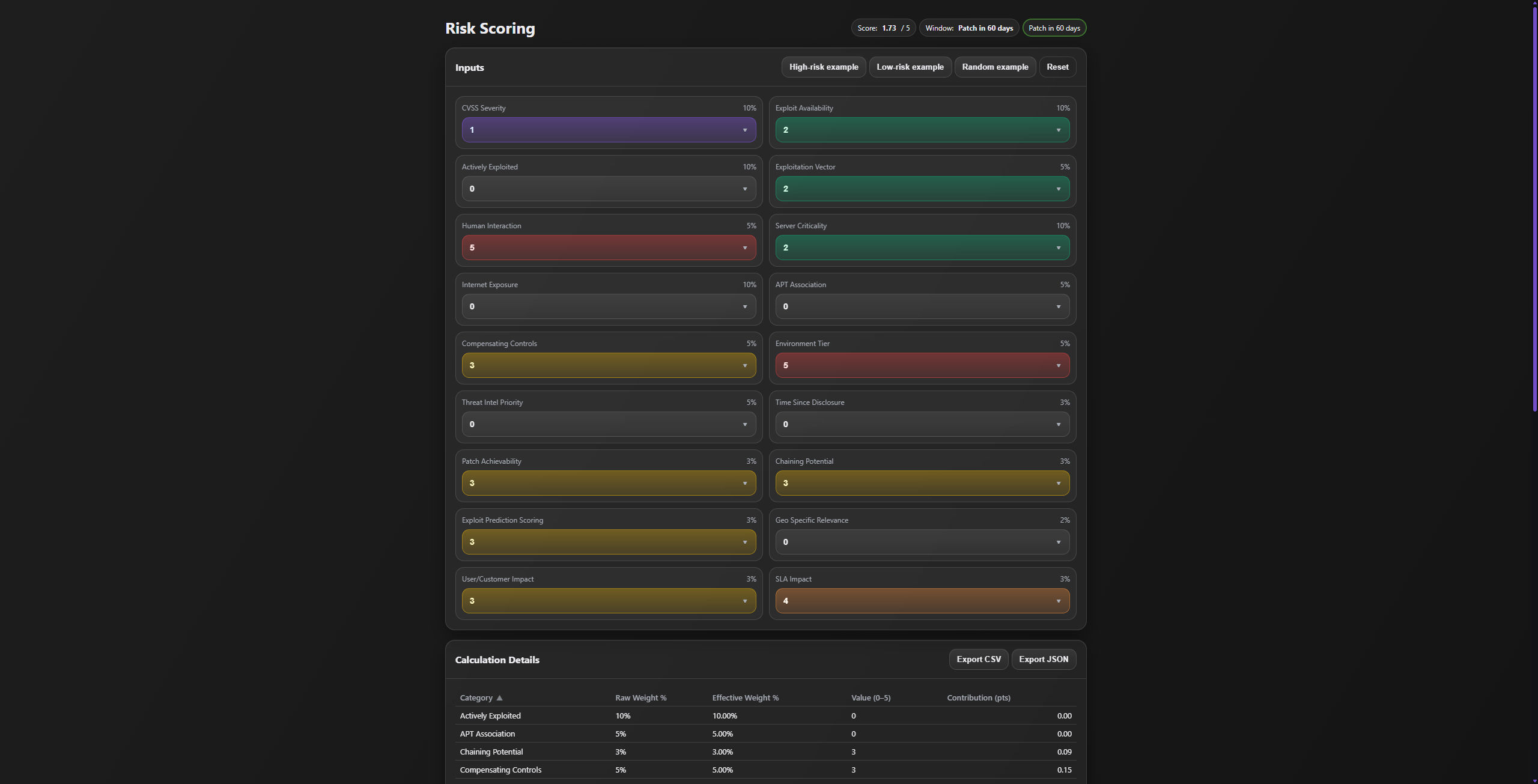
Browser-based KQL configurator with typed schema generation, placeholders, conditionals, local persistence, and secure exports (AES/XTEA/RSA hybrid).
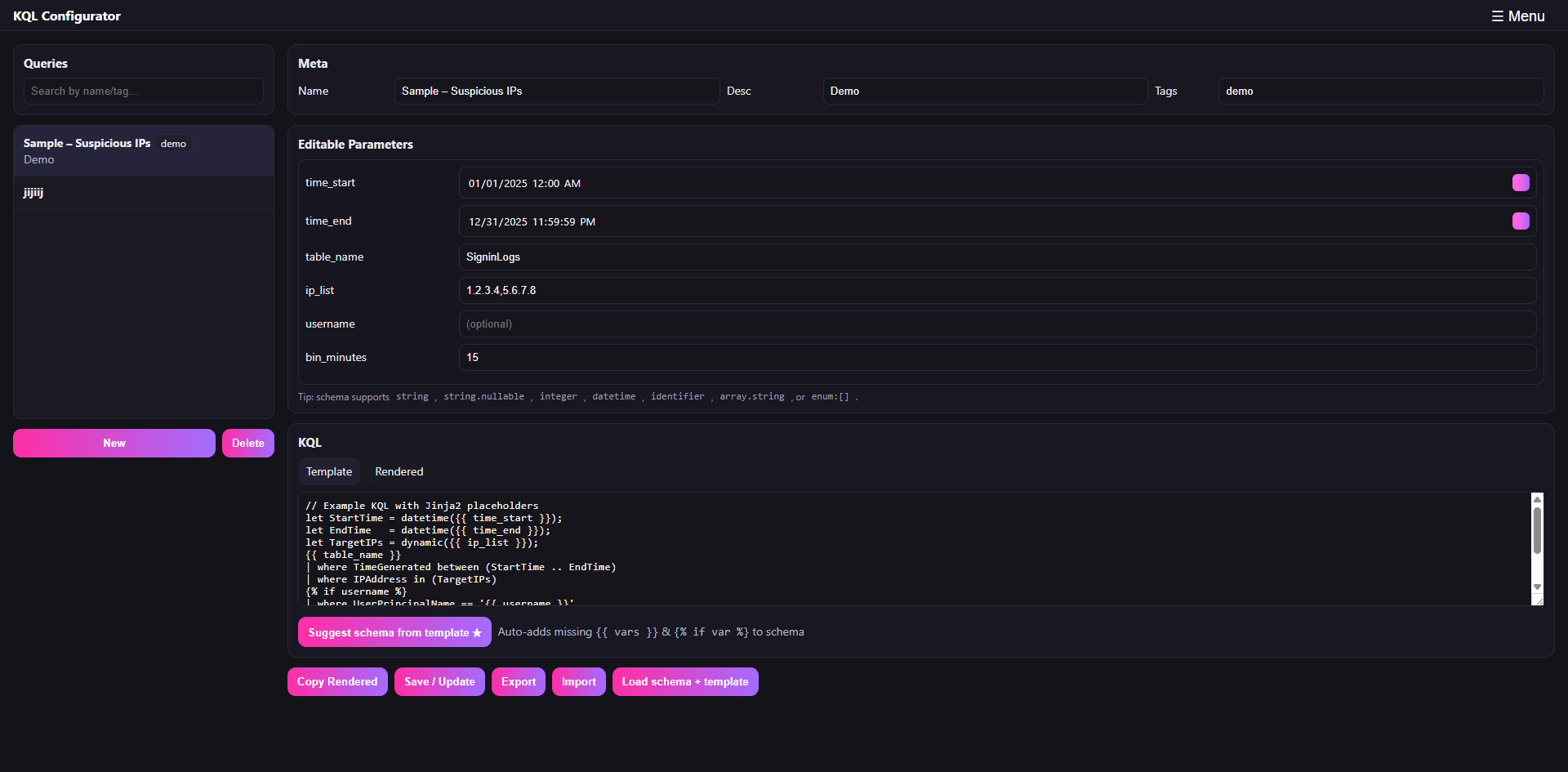
Decompile Android app → identify UUIDs, TEA key, encrypted command format. Rebuilt control flow in Python and validated behaviour on-device.
This section goes deeper: each node maps to a real project — tools, scripts, overlays, homelab builds, and coursework pieces that were actually useful. Click around the tree to see the story behind each item, including tech used, screenshots, and links.
I host my own CTF-style challenges alongside these writeups. No walkthroughs. No hints unless you earn them. Just you, the target, and whatever tools you trust. Rules are on the CTF page
I treat CTFs as an excuse to dive into tools, protocols, and weird edge cases you don't always hit in normal work. Pick a path (TryHackMe, HackTheBox, NZCSC) to see examples of web, pwn, forensics, and network challenges I've worked through.